Create feature-rich windows applications with many new components and universal dialogs.
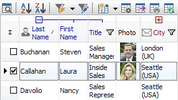
- improved DBGrid
- new DBRecordView, DBTreeView
- toolbars and db dialogs to Find, Filter, Sort, Export, Print...
- StringGrid with columns definition
- GroupBox with automatic alignment and resizing of owned controls
And many more from $25 to $95 only - click for details!
| A B C D E F G H I J K L M N O P Q R S T U V W X Y Z Other |